
What is a customer deployment platform? A guide for developers and SaaS vendors
A customer deployment platform is a system for deploying and managing software in a customer-controlled environment, whether that means a developer's own cloud account or a software vendor's customer's infrastructure. The term is used in at least two distinct contexts: teams that want to run workloads in their own cloud rather than a shared platform, and software vendors that need to deploy and operate their product inside their customers' cloud environments.
The term "customer deployment platform" does not have a single agreed definition. Depending on who is using it, it can refer to a PaaS that runs inside a team's own cloud account, or a platform a software vendor uses to deploy and manage their product inside their customers' environments. Both are valid uses of the term, and both are covered in this article.
This guide covers what a customer deployment platform involves across both use cases, who uses them, how they differ from general deployment platforms, and what to look for when evaluating one.
- "Customer deployment platform" covers at least two distinct use cases: a platform teams use to deploy their own workloads in their own cloud account, and a platform vendors use to deploy their software inside their customers' cloud environments.
- For developers and engineers, a customer deployment platform provides a consistent deployment layer on top of their own cloud infrastructure, giving them a managed developer experience while keeping workloads, data, and costs within their own cloud account.
- For SaaS vendors, a customer deployment platform handles the operational complexity of deploying and managing software across many customer environments, including on-premises, BYOC (Bring Your Own Cloud), and air-gapped infrastructure.
- The key distinction from a general deployment platform is where workloads run. General platforms host workloads in the provider's shared infrastructure. Customer deployment platforms run workloads in the customer's own cloud account or on-premises environment.
- Northflank supports both use cases: developers and teams can deploy in their own AWS, GCP, Azure, or on-premises infrastructure via BYOC, and SaaS vendors can deploy and manage their software inside their customers' cloud environments via Northflank's customer VPC deployment offering. Northflank is SOC 2 Type II certified.
Engineering teams looking to run workloads in their own cloud rather than a shared PaaS, and SaaS vendors needing to deploy their product inside their customers' environments, share the same underlying question: how do you get software running in a specific cloud account and keep it operating reliably over time?
A customer deployment platform is a system that provides the deployment, orchestration, and operational layer for software running in a customer-controlled environment. What distinguishes it from a general deployment platform is that the infrastructure belongs to the customer, not the platform provider.
The term covers at least two architecturally distinct use cases:
In this context, the customer is the team or organisation using the platform. An engineering team wants to run their workloads in their own AWS, GCP, Azure, or on-premises environment rather than in a provider's shared infrastructure.
A customer deployment platform in this sense is a managed layer that sits on top of the team's own cloud account and handles deployment orchestration, Kubernetes lifecycle management, CI/CD pipelines, and developer tooling. The team brings the cloud; the platform manages the workload and deployment layer on top of it.
In this context, the customer is the vendor's paying customer. A SaaS vendor or ISV (independent software vendor) needs to deploy and manage their product inside their customers' cloud accounts or on-premises environments.
Enterprise customers in regulated industries often require software to run within their own cloud boundary rather than in a vendor-hosted SaaS environment. In this sense, a customer deployment platform provides the control plane the vendor uses to provision, deploy, update, and monitor their software across many customer environments through a single interface.
Both use cases share the same underlying principle: workloads and, in most configurations, data run in the customer's environment rather than the platform provider's.
The use cases above map to three distinct audiences, each with different requirements.
Teams that want to run workloads in their own cloud account rather than a shared PaaS.
Common reasons include data residency requirements, cost optimisation through existing cloud commitments and reserved instance pricing, security and compliance policies that restrict where workloads can run, and avoiding dependence on a single provider's shared infrastructure.
These teams want the developer experience of a managed PaaS but need the workloads to stay within their own cloud boundary.
Software vendors whose enterprise customers require software to run within their own cloud account rather than in vendor-hosted SaaS.
This is common in financial services, healthcare, government, and other regulated industries where data sovereignty, compliance frameworks, or internal security policies restrict the use of third-party hosted software.
Supporting this at scale, across many customers on different cloud providers, becomes difficult to manage without a platform that handles provisioning, CI/CD, observability, and configuration management across customer environments.
Internal DevOps or platform engineering teams building tooling for their own engineering organisation.
They need workloads to run within their company's own cloud boundary for security, compliance, or cost reasons, but want a consistent developer experience across teams rather than raw Kubernetes or bespoke IaC.
The table below outlines the key differences:
| General deployment platform | Customer deployment platform | |
|---|---|---|
| Where workloads run | Provider's shared infrastructure | Customer's own cloud account or on-premises |
| Where data lives | Provider's environment | Customer's environment |
| Infrastructure management | Fully managed by provider | Customer brings infrastructure, platform manages workloads |
| Data residency and compliance | Depends on provider's certifications | Customer controls their own boundary |
| Cost model | Provider charges for compute and storage | Customer uses their own cloud account and existing commitments |
The key tradeoff is control versus simplicity. General deployment platforms are simpler to get started with since the provider handles all infrastructure. Customer deployment platforms give teams and vendors more control over where workloads run and where data lives, at the cost of managing the underlying cloud infrastructure themselves or bringing it to the platform.
The specific capabilities vary between platforms. The following are among the things worth evaluating when assessing a customer deployment platform:
When deploying across AWS, GCP, Azure, or on-premises, the platform should provide a consistent developer experience regardless of the underlying infrastructure. Teams should not need to learn separate workflows per cloud provider, and vendors deploying across many customer environments should be able to manage all of them from a single interface.
Automated build, test, and deployment pipelines that work within the customer's cloud environment. Support for progressive rollouts, canary deployments, and rollback on failure. For SaaS vendors, this also means the ability to target specific customer environments for updates without a manual process per customer.
Many modern customer deployment platforms build on Kubernetes as the runtime layer. The platform should handle cluster provisioning and lifecycle management, so teams do not have to manage Kubernetes cluster operations directly. Support for managed Kubernetes services such as EKS on AWS, GKE on GCP, and AKS on Azure is worth verifying for multi-cloud use cases.
Metrics, logs, and health signals collected within the customer's environment. For SaaS vendors managing many customer deployments, observability needs to work across all environments without the vendor accessing application-level customer data. This typically requires separation at the logging and metrics layer.
For SaaS vendors supporting multiple customer environments, the platform needs to maintain isolation between customer deployments. This typically involves dedicated infrastructure per customer, namespace separation, encrypted secrets, and network policies. Hard isolation is designed to prevent one customer's workload from accessing another's.
Audit trails, RBAC, mTLS service mesh, and encryption at rest and in transit. For enterprise teams and vendors operating in regulated industries, these are often baseline requirements rather than optional features.
Northflank addresses both use cases described in this article through two related but distinct products.
Northflank's BYOC product provides a managed platform layer on top of the customer's own AWS, GCP, Azure, Oracle, or on-premises infrastructure. The team or organisation brings their cloud account or existing Kubernetes cluster; Northflank manages the platform layer, including deployment pipelines, services, databases, and workloads on top of it.
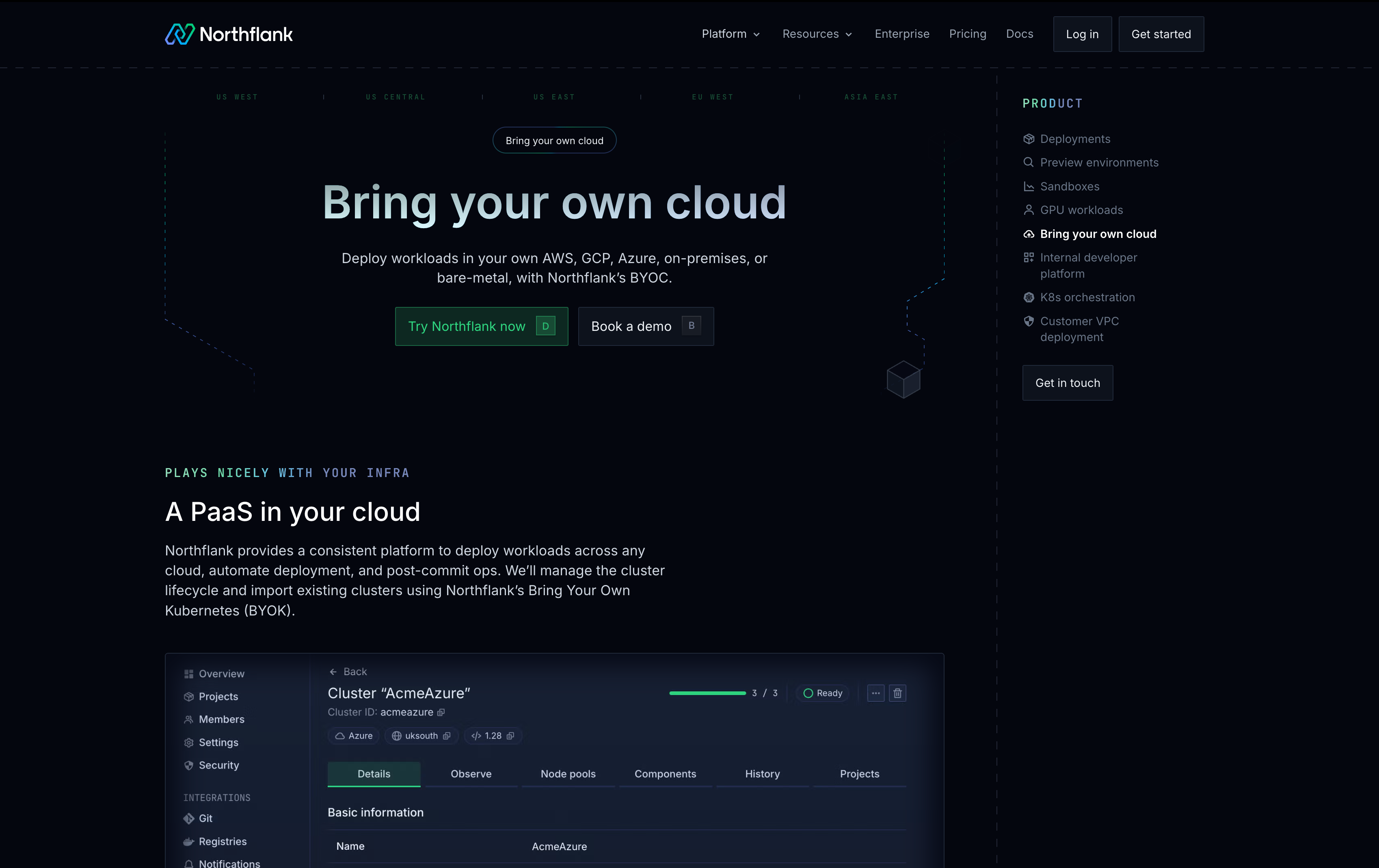
The developer experience is consistent across all environments. Northflank's UI, CLI, and API work the same way regardless of the underlying cloud, and features like preview environments, stateful workloads, and release pipelines are available across all clouds. Teams can also run across multiple cloud providers simultaneously from a single interface.
This suits engineering teams that want a managed PaaS experience while keeping workloads within their own cloud boundary, as well as enterprise teams that need to consolidate infrastructure management across multiple cloud accounts.
Northflank's customer VPC deployment product provides a control plane for SaaS vendors deploying and managing their application directly inside their customers' cloud environments. Vendors define their application once and Northflank handles provisioning, CI/CD, monitoring, and update delivery across their customers' AWS, GCP, Azure, Oracle, and on-premises environments from a single interface.
Each customer deployment runs on dedicated infrastructure with namespace-level separation, mTLS, encrypted secrets, and network policies applied by default. New customer environments can be provisioned in minutes, reducing what would otherwise take weeks of manual setup. Northflank's control plane connects to customer environments through secure cross-account links without credential sharing.
Vendors can get started directly (self-serve) or book a session with an engineer for teams with specific infrastructure or compliance requirements.
See the following guides for more on deploying software in customer environments, implementation approaches on AWS, and the software distribution layer:
- SaaS deployment in customer environments: why enterprise customers require software to run in their own environments and the key deployment models
- Deploying SaaS in a customer VPC: a technical walkthrough of implementation approaches on AWS, including AWS PrivateLink, in-VPC deployment, and VPC Lattice
- Software distribution platforms: the software distribution layer, including licensing, packaging, delivery, and distribution models
A traditional PaaS runs workloads on the provider's shared infrastructure. A customer deployment platform runs workloads in the customer's own cloud account or on-premises environment. The key difference is where the compute, storage, and data reside. Some platforms, like Northflank, offer both options: a managed cloud where the provider hosts everything, and a BYOC mode where the customer brings their own infrastructure.
BYOC stands for Bring Your Own Cloud. In the context of a deployment platform, it means the customer provides their own cloud account or Kubernetes cluster, and the platform deploys and manages workloads within it. The customer retains control over the underlying infrastructure while the platform handles the operational layer on top.
Some customer deployment platforms support air-gapped deployments, where the customer environment has no internet connectivity. This typically requires offline distribution methods such as downloadable installation bundles and local registry setup. Not every platform supports air-gapped environments, so this is worth verifying if your customers operate in restricted network environments.
Deploying in your own cloud means running your team's or organisation's workloads in your own AWS, GCP, Azure, or on-premises account. Deploying in your customer's cloud means a software vendor running their product inside their customer's cloud account. Both involve customer-controlled infrastructure, but the relationship is different: in the first case the team is both the customer and the operator, in the second the vendor operates software on behalf of their customer inside that customer's environment.
This varies by platform. Common cloud providers supported include AWS, GCP, and Azure. Some platforms, like Northflank, also support Oracle Cloud, Civo, CoreWeave, bare-metal, and on-premises Kubernetes distributions. Multi-cloud support is worth verifying if your customers are distributed across different providers or if you need to support on-premises deployments.