![Header image for blog post: What is a sandbox environment? [2026 guide]](https://assets.northflank.com/what_is_a_sandbox_environment_2b4cc349ea.png?auto=avif&quality=100&width=937)

What is a sandbox environment? [2026 guide]
A sandbox environment is one of those concepts that sounds simple until you need to implement it at scale. The core idea is consistent: give code a place to run that cannot affect anything outside its defined boundary.
What varies is the implementation, and the right implementation depends heavily on what you're sandboxing and why.
This article covers what a sandbox environment is, the main isolation models available in 2026, how to choose between them, the operational challenges you'll run into in production, and a recommended platform for running sandboxes at scale.
- A sandbox environment is an isolated runtime that lets you execute code, test changes, or run untrusted workloads without affecting your production systems or other users' data.
- Sandboxes exist on a spectrum. At one end, you have lightweight process-level isolation for quick integration testing. At the other, you have microVM-based runtimes with hard resource limits and network restrictions, which are now the standard for safely executing AI-generated code.
- The key considerations are isolation strength, cold start latency, support for both ephemeral and persistent workloads, and whether you can run sandboxes inside your own infrastructure.
Platforms like Northflank provide secure sandbox infrastructure with microVM and advanced runtime isolation (Firecracker, gVisor, Kata), both ephemeral and persistent execution modes, and bring-your-own-cloud support, so you can run sandboxed workloads inside your own VPC rather than a third-party managed cloud.
A sandbox environment is an isolated execution context where code runs without access to resources, data, or network segments outside its defined scope, unless you explicitly allow it.
You'll encounter sandboxes across several distinct use cases:
- Development and testing: Run feature branches against a copy of production services without touching live data.
- Security research: Execute suspicious files or code in an isolated VM to observe behavior safely.
- Multi-tenant platforms: Isolate each customer's workload so one tenant's code or resource usage cannot affect another's.
- AI agent execution: Autonomous agents generate and run code dynamically. That code is untrusted by default, even if your own model wrote it.
All of these share the same requirement: enforceable boundaries between what runs inside and what exists outside.
Isolation is implemented at different layers of the stack, and the layer you choose determines both your security guarantees and your operational overhead.
Containers use Linux namespaces and cgroups to enforce boundaries at the OS level. They're fast to start and cheap to run, but they share the host kernel. A kernel vulnerability can break the isolation boundary entirely.
Advanced isolation runtimes sit between containers and full VMs. Firecracker and Kata use microVM-based isolation, while gVisor takes a different approach entirely, running a userspace kernel that intercepts all syscalls before they reach the host.
- Firecracker boots a lightweight VM using KVM with significantly lower overhead than a full VM.
- gVisor intercepts syscalls in userspace before they reach the host kernel
- Kata Containers run containers inside lightweight VMs with separate kernels
These runtimes are the current standard for running untrusted code at scale. The isolation is strong enough to mitigate most kernel exploits, and the startup overhead is acceptable for production workloads.
Full VMs run each sandbox in a separate guest OS with its own kernel. Isolation is strongest here, but cold start times run into seconds, and memory overhead is significant. This is the right choice for malware analysis or workloads with hardware-level isolation as a compliance requirement.
Run sandboxes in your own infrastructure
If you're building on AI agents or running multi-tenant workloads, you need sandbox infrastructure that fits inside your existing stack.
Northflank provides secure sandboxes for running untrusted code at scale, with microVM and advanced runtime isolation (Firecracker, gVisor, Kata), both ephemeral and persistent execution modes, and the option to deploy entirely inside your own VPC.
Get started with Northflank or schedule a demo.
Related resources:
Choosing the right sandbox type comes down to your threat model and your tolerance for overhead.
| Isolation type | Mechanism | Security boundary | Typical use case |
|---|---|---|---|
| Container | Linux namespaces + cgroups | Shared kernel | Dev/test, low-risk workloads |
| gVisor | Userspace kernel | Userspace kernel boundary | Untrusted code, multi-tenancy |
| Firecracker microVM | KVM lightweight VM | Separate kernel | AI agent execution |
| Kata Containers | Container in lightweight VM | Separate kernel | Regulated workloads |
| Full VM | Hypervisor | Separate kernel + hardware | Malware analysis |
Sandboxes introduce real trade-offs you need to plan for, both upfront and in production.
- Cold start latency variance: Even microVMs have startup overhead. Quoted creation times often measure only the VM boot phase and exclude image pulls, network setup, and process initialization. Your real end-to-end time will be higher, and it will vary under load.
- Resource overhead at scale: Each sandbox carries baseline memory and CPU costs. At high concurrency, this compounds fast. You need precise resource limits and efficient scheduling to keep costs manageable.
- Network restrictions vs. functionality: Sandboxes work best with minimal network access, but many real workloads need outbound access to install packages or call APIs. Every allowlisted endpoint is a potential escape path.
- Persistent state complexity: Ephemeral sandboxes are simple: destroy them after use. Persistent sandboxes that maintain state across sessions require careful management of storage volumes, network identity, and lifecycle, and zombie environments that aren't properly garbage collected will accumulate and consume compute.
- Escape risks: No isolation model is unbreakable. Kernel vulnerabilities have been exploited to break out of containers. MicroVMs significantly raise the difficulty, but resource limits, network restrictions, and least-privilege configuration all reduce your attack surface.
Northflank provides secure sandboxes for running untrusted code at scale with microVM and advanced runtime isolation (Kata Containers, Firecracker, gVisor), supporting both ephemeral and persistent environments in managed cloud or your own VPC.
Northflank has been running secure sandboxes sandboxes in production since 2021 across startups, public companies, and government deployments. If you need GPUs, workers, APIs, or databases running alongside your sandboxes, they run in the same platform.
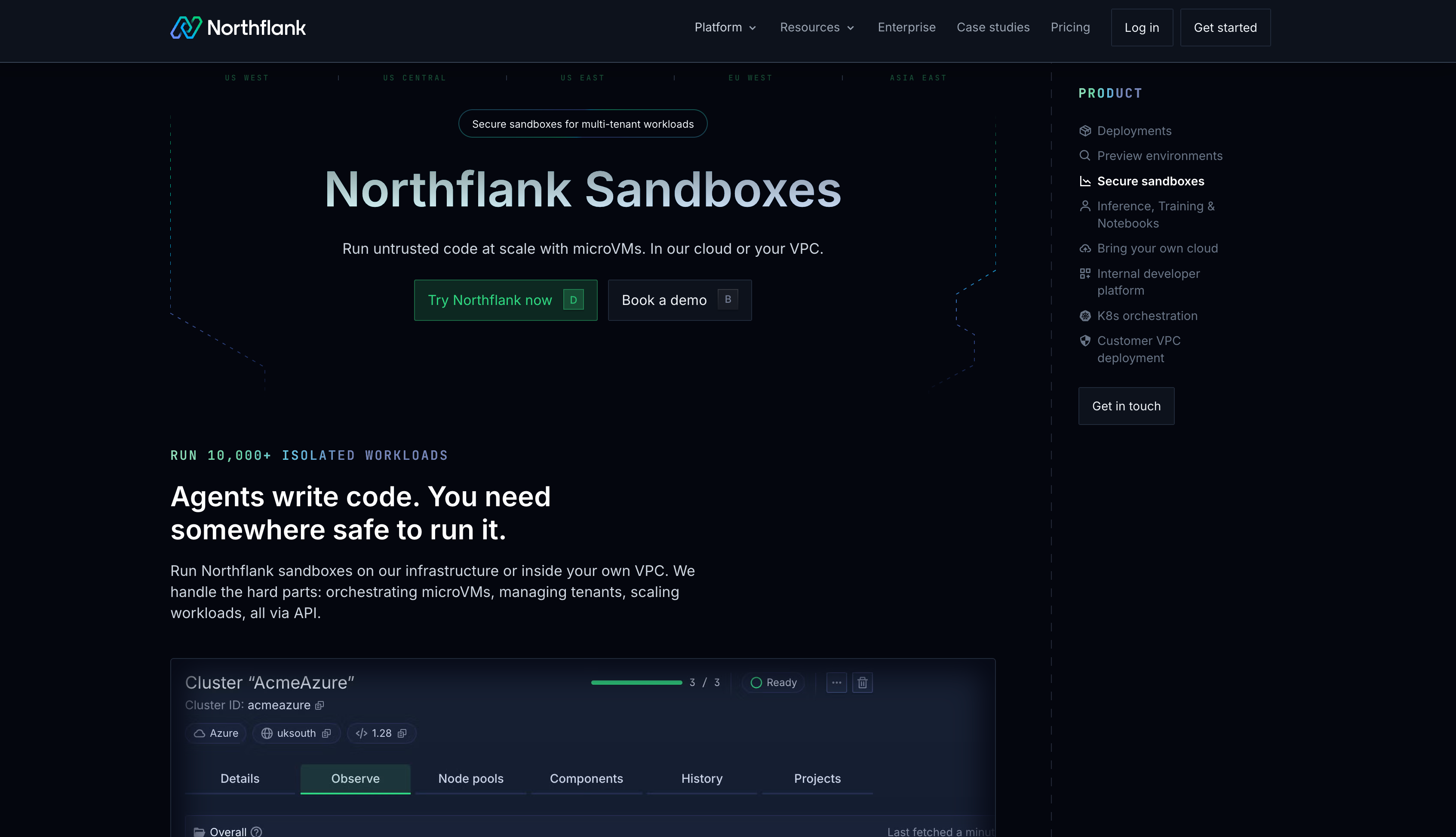
Here's what Northflank provides out of the box:
Northflank supports Firecracker, gVisor, and Kata Containers. You choose the isolation model based on your workload's security requirements, and Northflank handles the orchestration. End-to-end sandbox creation runs at 1-2 seconds, covering the full stack.
You get both. Ephemeral sandboxes for short-lived execution and persistent environments for stateful workloads like development environments, long-running agents, or user sessions that need to survive beyond a single request.
Most enterprise teams deploying sandboxed workloads can't accept their code or data leaving their own infrastructure. Northflank supports bring-your-own-cloud deployment inside your own VPC on AWS, GCP, Azure, Oracle Cloud, CoreWeave, Civo, bare-metal, and on-premises, and it's available self-serve.
You can run APIs, background workers, databases, and AI agent infrastructure alongside your sandbox pool on the same platform. GPU workloads are supported with on-demand provisioning and no quota requests.
Sandboxes are accessible via API, CLI, and SSH. CPU at $0.01667/vCPU-hour, memory at $0.00833/GB-hour. Full pricing, including GPUs, is on the Northflank pricing page.
The right sandbox approach depends on your threat model and workload type. Work through these questions:
- Who controls the code? If it's trusted code from your own engineers, container-level isolation is likely sufficient. If it's AI-generated or user-submitted, use microVM isolation. The overhead is worth it.
- Ephemeral or persistent? If your use case requires session state across requests, confirm your platform supports persistent sandboxes, not just fire-and-forget execution.
- Where does the code run? If you have data residency requirements or can't send code to a third-party cloud, BYOC deployment is a hard requirement.
- What's your scale? At low request volume, a simple container pool works. At high concurrency with burst traffic, you need pre-warming, efficient scheduling, and per-sandbox resource enforcement.
A Firecracker microVM that spins up when an AI agent needs to execute generated Python code, runs it with no outbound network access and a defined memory cap, returns the output, and is destroyed after the session. Another example: a per-developer environment that mirrors production services but has no access to production data.
The term comes from the physical concept of a sandbox: a bounded area where you can experiment freely without the mess spreading to the surrounding environment. In software, it maps to an isolated execution context where changes and side effects are contained.
A test environment is a deployment stage used for running automated tests before releasing to production. A sandbox is about execution isolation for safety or tenancy reasons. You can run tests inside a sandbox, but a staging environment running trusted code is not a sandbox in the security sense.
The main types are process-isolated containers, gVisor (userspace kernel), microVMs (Firecracker, Kata), and full VMs. Each trades isolation strength for startup speed and resource overhead. MicroVMs are the current standard for untrusted code execution.
Yes. Kernel vulnerabilities have been used to break out of container-based sandboxes. MicroVMs significantly raise the difficulty by providing a separate kernel, but no isolation model is unbreakable. Defense-in-depth, combining strong isolation with network restrictions, resource limits, and least-privilege config, is the right approach.