

Remote code execution sandbox: secure isolation at scale (2026 guide)
Running untrusted code is now a core requirement for AI agents, developer tools, automation platforms, CI systems, and user-defined workflows. If your product allows external input to execute logic, you are operating a remote code execution surface.
This guide explains what a remote code execution sandbox is, how isolation models differ, what security controls are required in production, and how to evaluate platforms without oversimplifying the tradeoffs.
A remote code execution sandbox is an isolated runtime environment that allows untrusted or user-submitted code to execute without exposing the host system, adjacent workloads, or sensitive infrastructure.
A production-grade sandbox enforces:
- Filesystem isolation: Prevents access to host files and secrets.
- Process isolation: Stops interference with other workloads.
- Network isolation: Restricts outbound and internal connectivity.
- Kernel isolation: Reduces the blast radius of privilege escalation attempts.
Isolation can be implemented using hardened containers, syscall interception such as gVisor, or microVM-based virtualization such as Firecracker and Kata Containers.
Northflank provides microVM-backed remote code execution sandboxes using Firecracker, gVisor, and Kata, with both ephemeral and persistent execution modes and bring-your-own-cloud support across AWS, GCP, Azure, Civo, Oracle Cloud, CoreWeave, and on-premise or bare metal deployments.
A remote code execution sandbox is a controlled execution boundary where code originating outside your trusted system runs inside restricted limits.
“Remote” refers to the source of the code. It may come from:
- End users submitting scripts
- AI agents generating tool calls
- API consumers uploading logic
- CI/CD pipelines running builds from external contributors or unreviewed sources
- Plugin ecosystems extending your application
The sandbox enforces boundaries so that this code cannot:
- Read sensitive files from the host
- Access internal services
- Escalate privileges
- Persist malicious changes across sessions
This is distinct from a remote code execution (RCE) vulnerability, which is an unintended exploit path. A remote code execution sandbox is intentional execution with controlled isolation.
Executing user-submitted or generated code directly on shared infrastructure exposes your system to multiple failure modes.
The required isolation level scales with the trust level of the code source. A pipeline running version-controlled internal code carries a different risk profile than a platform executing LLM-generated or user-submitted scripts.
Without isolation:
- Filesystem access: Code can read environment variables, credentials, or configuration files.
- Network access: Code can exfiltrate data or access internal metadata endpoints.
- Kernel exposure: Standard containers share the host kernel, which expands the impact of kernel-level exploits.
- Persistence: Reused environments allow state to survive across executions.
- Resource exhaustion: CPU, memory, and I/O abuse can disrupt other tenants.
These risks compound in multi-tenant systems or AI-driven platforms where code is generated dynamically.
Different isolation approaches provide different kernel boundaries and operational tradeoffs.
Containers isolate workloads using namespaces and cgroups, but share the host kernel.
A hardened container configuration includes:
- Syscall filtering: Restrictive seccomp profiles reduce the available syscall surface.
- Capability reduction: Remove elevated Linux capabilities unless explicitly required.
- Read-only root filesystem: Prevent base image mutation.
- cgroup enforcement: Apply CPU and memory constraints.
- Network restrictions: Enforce default-deny egress policies.
Containers are efficient and widely supported. The architectural limitation is kernel sharing, which increases the impact if a kernel vulnerability is exploited.
gVisor intercepts syscalls in user space, reducing direct interaction with the host kernel.
Characteristics include:
- Reduced kernel exposure compared to standard containers.
- Compatibility with existing container workflows.
- Increased syscall latency, kernel feature compatibility gaps, and an additional attack surface from the interception layer.
This approach fits environments where container isolation is insufficient, but full virtualization per workload is not required.
MicroVMs use hardware virtualization to provide a separate guest kernel per workload.
Technologies such as Firecracker and Kata Containers create lightweight virtual machines designed for high-density workloads.
With microVM-based sandboxes:
- Each execution runs with its own guest kernel.
- Virtualization boundaries isolate workloads at the hypervisor level.
- A guest kernel compromise does not directly expose the host kernel, but the hypervisor remains part of the attack surface.
For multi-tenant SaaS, LLM-generated code execution, and compliance-sensitive systems, microVM-based isolation is frequently chosen as the default boundary.
If you are evaluating remote code execution sandbox isolation for AI-generated or code-generation workloads, see the following guides:
- How to spin up a secure code sandbox and microVM using Firecracker, gVisor, and Kata: covers architecture decisions and isolation layers, not just surface configuration.
- Secure runtimes for codegen tools: microVMs, sandboxing, and execution at scale
- Best code execution sandbox for AI agents
Isolation models differ primarily in how they enforce kernel boundaries and limit blast radius.
| Model | Kernel boundary | Isolation mechanism | Host kernel exposure | Typical use case |
|---|---|---|---|---|
| Hardened containers | Shared | Namespaces + cgroups + seccomp | Direct | Internal or semi-trusted workloads |
| gVisor | Shared but intercepted | User-space syscall interception | Indirect | Moderately untrusted multi-tenant |
| MicroVM (Firecracker/Kata) | Separate guest kernel | Hardware virtualization | Indirect (via hypervisor boundary) | Untrusted or adversarial multi-tenant |
The deeper the kernel boundary, the smaller the blast radius if a workload is compromised. No isolation model eliminates risk entirely; isolation reduces blast radius and raises the cost of compromise.
Isolation mechanisms are only one layer of protection. A production-grade remote code execution sandbox relies on layered controls.
Core controls include:
- Syscall filtering: Reduce high-risk kernel interactions.
- Capability reduction: Remove unnecessary runtime privileges.
- Network isolation: Enforce default-deny outbound policies.
- Ephemeral execution: Reset environments between runs.
- Resource limits: Apply CPU, memory, and I/O quotas.
The objective is consistent enforcement of least privilege across runtime, network, and storage layers.
Sandbox workloads vary. Some require clean, single-use execution, while others need long-running state.
- Ephemeral environments: Short-lived execution pools destroyed after each run. Suitable for user-submitted scripts and AI-generated tool calls where isolation between executions is critical.
- Persistent environments: Long-running stateful services with attached volumes, databases, or background workers. Suitable for agents, APIs, and orchestration layers that maintain state over time.
Modern platforms like Northflank increasingly support both models.
Northflank supports short-lived execution pools as well as long-running stateful services within the same platform, allowing teams to run isolated sandbox executions alongside persistent agents, APIs, and supporting infrastructure. Supporting both modes reduces architectural fragmentation as systems evolve from simple execution pipelines to full application runtimes.
Selecting a sandbox platform requires architectural and operational evaluation.
Key considerations include:
- Kernel boundary: Does the platform provide microVM-level isolation?
- Execution model: Are both ephemeral pools and persistent services supported?
- Bring your own cloud: Can you deploy inside your own VPC across major cloud providers such as AWS, GCP, Azure, or on-premise?
- Workload scope: Can agents, APIs, workers, and databases run alongside sandboxes?
- Multi-tenant design: Is tenant isolation enforced by default?
- Access model: Are API, CLI, and SSH interfaces available?
A production-ready remote code execution sandbox platform goes beyond basic workload isolation. It must provide durable isolation boundaries, support multi-tenant execution, integrate with surrounding infrastructure, and operate reliably at scale.
Northflank provides this model, combining microVM-based isolation with workload orchestration and bring-your-own-cloud deployment.
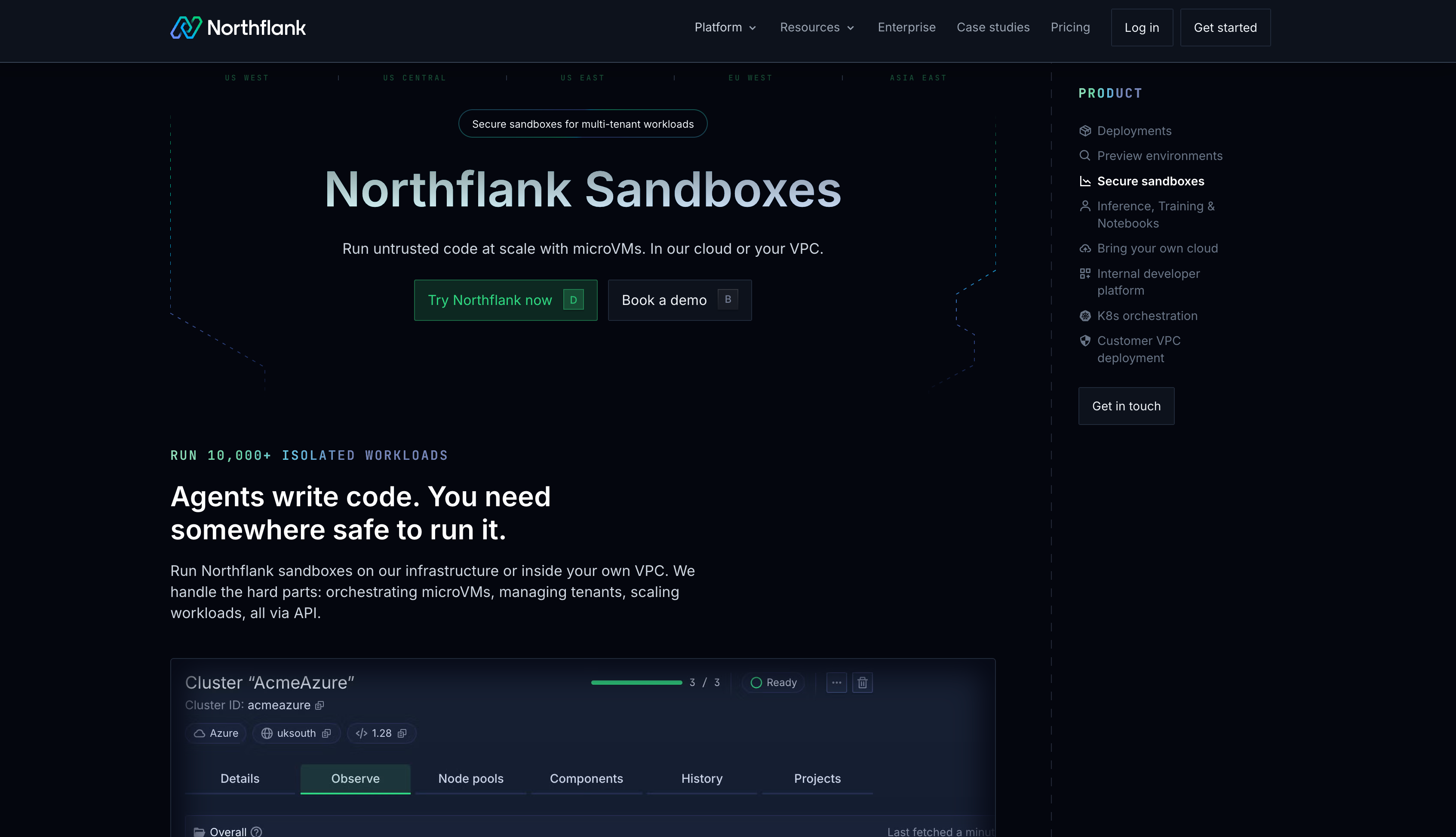
Key characteristics of Northflank sandboxes include:
- MicroVM isolation: Separate guest kernels for untrusted workloads using technologies such as Firecracker, Kata Containers, or gVisor.
- Ephemeral execution pools: Short-lived environments destroyed after each run to prevent state leakage.
- Persistent services: Long-running stateful workloads with attached volumes, databases, background workers, and APIs.
- Bring-your-own-cloud deployment: Support for running inside your own VPC across AWS, GCP, Azure, Civo, Oracle Cloud, CoreWeave, or on-premise and bare metal environments.
- Full workload runtime: Ability to run agents, APIs, workers, and supporting services alongside sandbox execution.
- GPU support: On-demand CPU and GPU provisioning without manual quota requests, relevant for teams running inference or training workloads alongside sandbox execution
Next steps for your remote code execution sandbox architecture
If you’d like a step-by-step architectural walkthrough, see how to spin up a secure code sandbox and microVM.
You can review deployment models and secure sandbox capabilities directly on Northflank. For teams with specific compliance, networking, GPU, or bring-your-own-cloud requirements, you can also book a demo to speak with an engineer.
This FAQ addresses common questions related to remote code execution sandbox architecture.
Sandboxed code execution is the practice of running code inside a restricted environment that limits its access to the host filesystem, network, processes, and kernel interfaces.
An RCE vulnerability is an unintended exploit that allows attackers to execute code. A remote code execution sandbox is an intentional execution boundary with enforced isolation controls.
Escape risk depends on the isolation model. Container-based sandboxes share the host kernel. MicroVM-based sandboxes use separate guest kernels, which reduces host exposure if a guest environment is compromised.
For internal or low-risk systems, hardened containers may be acceptable. For adversarial multi-tenant environments, microVM-level isolation is commonly preferred.