Kata Containers vs gVisor
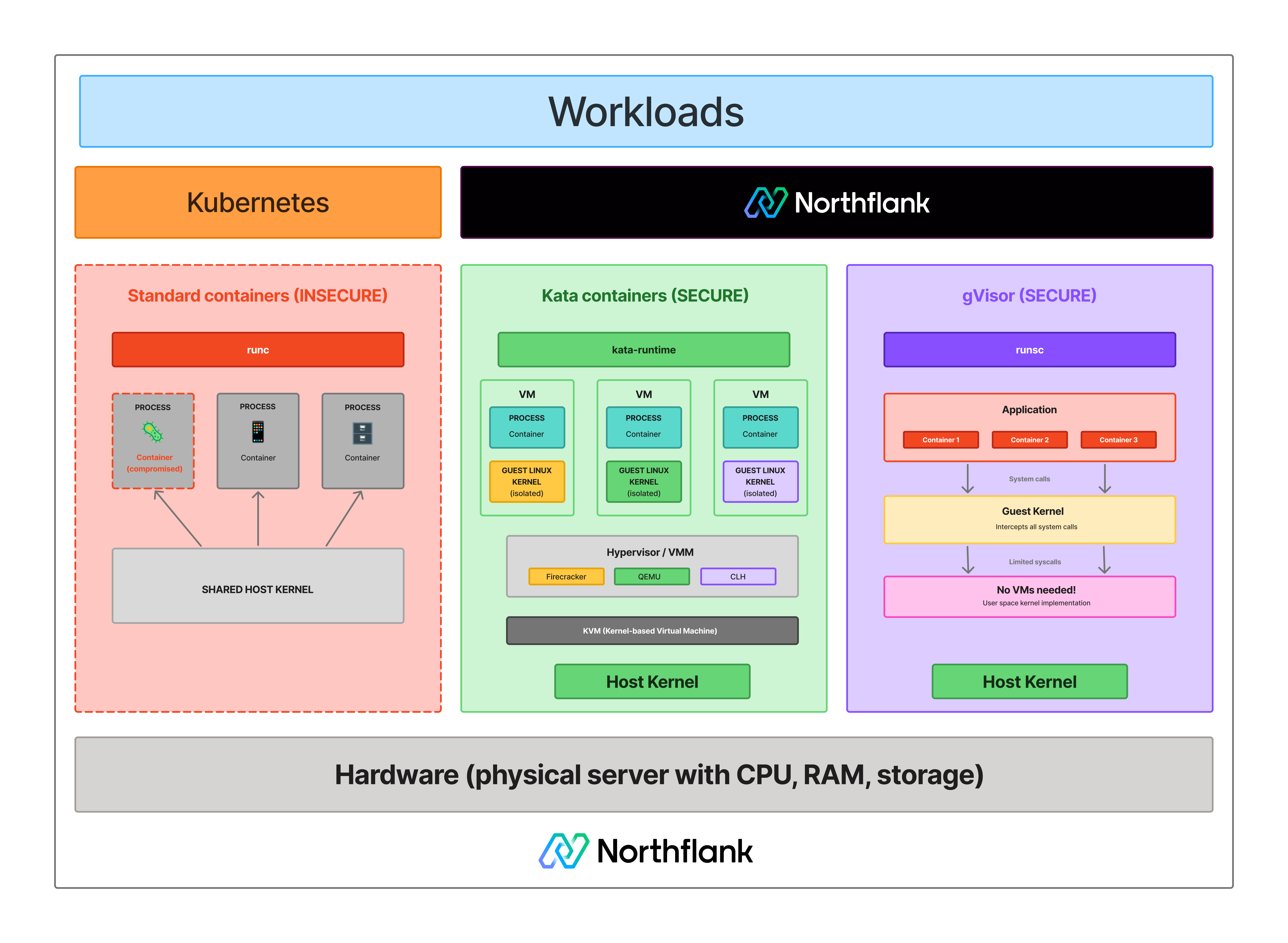
Kata Containers and gVisor both address the shared-kernel problem that standard containers leave unsolved. They take different architectural approaches, make different tradeoffs on isolation strength and overhead, and are suited to different environments and threat models.
This article compares Kata Containers and gVisor on architecture, isolation strength, performance, infrastructure requirements, and use case fit, and covers how Northflank runs both in production.
What is Northflank?
Northflank is a full-stack cloud platform that runs Kata Containers and gVisor in production alongside Firecracker and Cloud Hypervisor, applying the right isolation technology based on workload requirements. In production since 2021 across startups, public companies, and government deployments. Get started (self-serve) or book a session with an engineer for specific infrastructure or compliance requirements.
| Kata Containers | gVisor | |
|---|---|---|
| Type | Container runtime with VM-level isolation | Container runtime with syscall interception |
| Isolation model | Hardware-level (KVM via VMM) | Syscall interception (user-space kernel) |
| Kernel | Dedicated guest kernel per workload | No dedicated kernel (Sentry handles syscalls) |
| Hardware virtualisation required | Yes (KVM) | No (Systrap) / Optional (KVM mode) |
| Boot time | ~150ms to ~300ms depending on VMM and configuration | Milliseconds |
| I/O overhead | Near-native | Syscall tax on I/O-heavy workloads |
| Syscall compatibility | Full Linux | Most syscalls, some gaps |
| Kubernetes integration | Native via CRI / RuntimeClass | Via RuntimeClass (runsc) |
| Operational complexity | Higher (VMM backend required) | Lower (drop-in OCI runtime) |
| Best for | Adversarial multi-tenant workloads, untrusted code | Enhanced container security, no nested virtualisation |
Kata Containers is an open-source container runtime that runs workloads inside lightweight virtual machines, integrating natively with Kubernetes via the Container Runtime Interface. It is maintained under the OpenInfra Foundation and supports Cloud Hypervisor (default), Firecracker, and QEMU as VMM backends.
Each workload gets its own dedicated Linux guest kernel, enforced by hardware virtualisation via KVM. Kata is not itself a VMM; it is the orchestration layer that makes microVMs work with container tooling. From Kubernetes' perspective, a Kata-backed pod looks like a standard container. The isolation underneath is hardware-enforced. See What are Kata Containers? for a full technical breakdown.
gVisor is an open-source application kernel developed by Google that sandboxes containers by intercepting system calls in user space. Its core component, the Sentry, handles syscalls on behalf of the sandboxed workload without passing them to the host kernel. The Sentry is written in Go, a memory-safe language.
gVisor is not a VM. It does not boot a dedicated guest kernel per workload. In its default Systrap mode, it requires no hardware virtualisation. In KVM mode, it uses virtualisation hardware for address space isolation, but the sandbox retains a process model rather than booting a full guest OS. See What is gVisor? for a full technical breakdown.
This is the core tradeoff between the two technologies.
Kata Containers enforces isolation at the hardware level. Each workload boots its own Linux kernel inside a KVM boundary enforced by CPU hardware. To escape, an attacker must first compromise the guest kernel, then escape the KVM hypervisor layer. Those are two separate hardware-enforced barriers.
gVisor enforces isolation at the syscall level. The Sentry intercepts syscalls and handles them in user space, so the workload never reaches the host kernel directly. In Systrap mode, there is no hardware-enforced boundary. In KVM mode, virtualisation hardware is used for address space isolation, but the sandbox does not provide a dedicated guest kernel per workload.
For actively adversarial workloads where an attacker is specifically trying to escape the sandbox, Kata Containers provides the stronger guarantee. For workloads that need meaningfully better isolation than standard containers without the overhead or KVM requirements of microVMs, gVisor is a practical middle ground.
See how the two approaches compare against standard containers:
- Boot time: Kata Containers boots a guest kernel per workload, adding 150 to 300ms depending on VMM and configuration. gVisor starts in milliseconds with no kernel boot. For high-frequency, short-lived workloads, gVisor's startup advantage is meaningful.
- I/O overhead: gVisor's syscall interception adds latency on I/O-heavy workloads. Benchmarks suggest 10 to 30% slower than native containers depending on workload type. Kata Containers runs near-native I/O because the guest kernel handles syscalls directly. For databases, high-throughput file processing, or network-intensive workloads, Kata has a performance advantage.
- CPU-bound workloads: For CPU-bound workloads with infrequent syscalls, gVisor's overhead is minimal. The syscall tax only materialises on high-frequency syscall workloads.
- Memory overhead: Kata Containers carries the overhead of a VMM process and guest kernel per workload, though modern VMM designs keep this low. gVisor's Sentry adds per-sandbox overhead that is low but non-zero. Both are significantly lighter than traditional VMs.
Kata Containers requires KVM. The host must support Intel VT-x or AMD-V with KVM available. On cloud instances, the provider must support nested virtualisation for that instance type. Not all providers or instance types support this.
gVisor's Systrap mode requires no hardware virtualisation. It runs on any Linux host. This makes it the practical choice when nested virtualisation is unavailable, for example on certain cloud instance types or constrained environments. Its KVM mode optionally uses virtualisation hardware but does not require it.
For Kubernetes integration, both use RuntimeClass. Kata provides its runtime handler via kata-runtime. gVisor provides runsc. Both can run alongside standard container pods on the same cluster without changes to the control plane. See What is KVM? for more on the hardware requirements.
Kata Containers runs a full Linux guest kernel per workload. Syscall compatibility is not a concern; any workload that runs on Linux runs inside a Kata VM without modification.
gVisor's Sentry re-implements Linux system interfaces but does not cover every syscall. Applications that depend on less common or recently added syscalls may not behave correctly. Testing your specific workload under gVisor before deploying to production is important. For workloads with unusual syscall requirements, Kata is the safer choice.
Kata Containers requires more operational investment. A VMM backend must be configured and maintained, nested virtualisation must be available on the host, and Kata adds a layer of complexity on top of standard Kubernetes operations. For teams that need microVM isolation without building the orchestration layer themselves, platforms like Northflank abstract this complexity.
gVisor is closer to a drop-in replacement for the standard container runtime. You configure runsc as a RuntimeClass handler, reference it in your pod spec, and existing container images work without modification. The integration path is simpler than Kata.
Use Kata Containers when:
- Your threat model involves actively adversarial workloads where hardware-enforced isolation is required
- You are running untrusted code at scale (AI-generated outputs, customer-submitted scripts, multi-tenant platforms)
- Your workloads are I/O-heavy, and near-native performance is a requirement
- Your workloads have syscall requirements that gVisor does not cover
- KVM and nested virtualisation are available on your host
Use gVisor when:
- Nested virtualisation is unavailable on your host
- You want meaningfully stronger isolation than standard containers without microVM overhead
- Your workloads start and stop frequently, and millisecond startup matters
- Your workloads are CPU-bound with low syscall frequency
- You want a simpler integration path with existing Docker and Kubernetes workflows
See Kata Containers vs Firecracker vs gVisor for a three-way comparison that also covers Firecracker directly.
Northflank uses Kata Containers with Cloud Hypervisor as its primary approach for microVM isolation, with gVisor applied where syscall-interception isolation is sufficient or where nested virtualisation is unavailable. Firecracker is applied for workloads that benefit from its minimal device model. The platform has been in production since 2021 across startups, public companies, and government deployments.
Sandboxes spin up in approximately 1 to 2 seconds, with compute pricing starting at $0.01667 per vCPU per hour and $0.00833 per GB of memory per hour. See the pricing page for full details.
Northflank supports both ephemeral and persistent sandbox environments on managed cloud or inside your own VPC, self-serve into AWS, GCP, Azure, Oracle, CoreWeave, Civo, on-premises, or bare-metal via bring your own cloud.
Get started with Northflank sandboxes
- Sandboxes on Northflank: overview and concepts: architecture overview and core sandbox concepts
- Deploy sandboxes on Northflank: step-by-step deployment guide: step-by-step deployment guide
- Deploy sandboxes in your cloud: BYOC deployment guide: run sandboxes inside your own VPC
- Create a sandbox with the SDK: programmatic sandbox creation: programmatic sandbox creation via the Northflank JS client
Get started (self-serve), or book a session with an engineer if you have specific infrastructure or compliance requirements.
Kata Containers provides stronger isolation. Each workload boots a dedicated Linux guest kernel inside a KVM-enforced hardware boundary. For an attacker to escape, they must compromise the guest kernel and then escape the hypervisor layer. gVisor's Systrap mode does not have a hardware-enforced boundary. Its KVM mode uses virtualisation hardware for address space isolation but does not boot a dedicated guest kernel per workload.
No. gVisor's Systrap mode runs on any Linux host without KVM support. Its KVM mode optionally uses virtualisation hardware for better performance but does not require it. Kata Containers requires KVM on the host.
Yes. Both integrate via RuntimeClass. You can run Kata-backed pods, gVisor-backed pods, and standard container pods on the same cluster simultaneously by assigning different RuntimeClasses to different workloads.
For startup time, yes. gVisor starts in milliseconds with no kernel boot. Kata Containers takes 150 to 300ms, depending on VMM and configuration. For I/O-heavy workloads at runtime, Kata is faster because syscall interception in gVisor adds latency that does not exist in a microVM. For CPU-bound workloads, the runtime difference is minimal.
Yes. Kata Containers is OCI-compatible. Existing container images run inside Kata VMs without modification. The runtime changes. The image format does not.
Firecracker is a VMM that creates microVMs. Kata Containers is an orchestration framework that can use Firecracker as one of its VMM backends. Kata adds the CRI integration, VM lifecycle management, and Kubernetes compatibility that Firecracker alone does not provide. See What are Kata Containers? and What is AWS Firecracker? for full breakdowns.
- What are Kata Containers?: a full technical breakdown of Kata Containers' architecture, VMM backends, and Kubernetes integration
- What is gVisor?: how gVisor works, its components, execution platforms, and limitations
- Kata Containers vs Firecracker vs gVisor: a three-way comparison of the leading isolation technologies
- MicroVM vs gVisor: how the microVM model as a category compares to gVisor's syscall-interception approach
- What is a microVM?: how microVMs work and which technologies implement them
- What is KVM?: the hardware virtualisation layer Kata Containers builds on
- Firecracker vs gVisor: a focused comparison of Firecracker specifically against gVisor
- Containers vs virtual machines: the broader isolation landscape in context